Communicating over BLE — Basics
BLE Communication Architecture
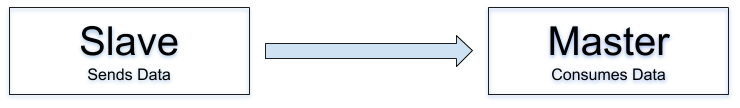
BLE communication is divided into two parties. The Slave has the data to be sent, and the Master receives and consumes the data. An example of a Slave is a sensor. An example of a Master is a smartphone (although a smartphone can be either Slave or Master, depending on the use case).
Security for Communication
Passive eavesdropping, wherein a third device could listen to the exchange between two other devices, was a problem in BLE until the implementation of AES-CCM encryption of data transferred using BLE.
The key exchange protocols, referred to as “pairing method” or “association model,” were subject to vulnerabilities that allowed hackers to decrypt the data.
The Pairing and Bonding method provides a passkey, a 6-digit number passed between the devices for connecting. The method offers a certain level of protection.
Sample Code from the Qualcomm® QCA4020 Development Board Application
BLE is initialized on the QCA4020/4024 Platform and it will start advertising after registering with the Services. In the following code snippet from the QCA4020 Development Board Application, the board registers with the Home Automation Service:
/QDN_ControlEndDevicesApp/spple/spple_demo.c”
InitializeBluetooth(0, 0);
QCLI_Parameter_t add_params[2];
memset(add_params, 0, sizeof(QCLI_Parameter_t)*2);
add_params[0].Integer_Is_Valid = 1;
add_params[0].Integer_Value = 1;
AdvertiseLE(1, add_params);
Now the QCA402x board is in the Advertising State, where other BLE-supported products can scan to get connected to it. Once the devices are in the Connection State, specific to the requirement and based on the defined Services, they can interact with each other.
