Building and Flashing an Image for Secure Boot on the Qualcomm® QCA4020/4024 Platform
What is secure boot?
The boot path is a preferred attack vector. It is difficult to guard against attacks there because anti-malware can be disabled by malicious code that prevents it from loading entirely.
Secure boot is designed to protect the system against malicious code being loaded and executed early in the boot process, before firmware is loaded. In secure boot, OS boot images and code are authenticated against the hardware before they are used in the boot process. The hardware is set up beforehand in a way that it authenticates only the code generated using security credentials you trust. Secure boot ensures that the boot image and firmware are as the manufacturer intended and have not being altered by malware or bad actors.
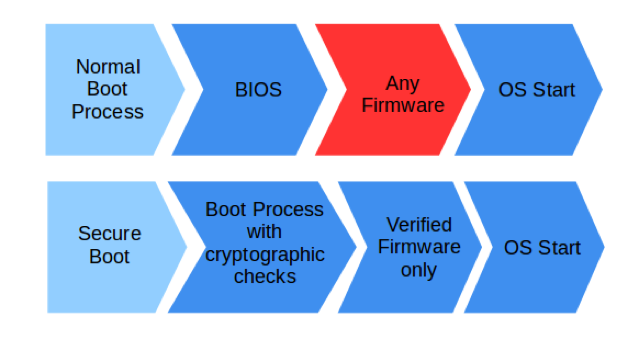
The difference between a normal boot process and secure boot
Enabling secure boot on the QCA402x board
In secure boot, keys are generated from your SSL certificate, hashed and burned into the CPU in a One Time Programmable (OTP) process. Once a key has been burned into the processor, it cannot be changed.
Building and flashing OTP programmer
Three device profiles are available in building OTP:
- Development profile
- Production test profile
- Production profile
In the code snippet below, we use the development profile:
- Edit the configuration file,
\target\quartz\mfg\OTP\tools\otp_config.xml, with model_id, pk_hash, and otp_profile as shown.<otp_descriptor>\ <firmware_region_write_disable>0</firmware_region_write_disable> <model_id>0x0</model_id> <pk_hash>de5480d49ed1cbe0813755f06324fce56e3eb391a9a40ffba8df9fd16c717744</pk_hash> <otp_profile>development</otp_profile> </otp_descriptor> - Build the QCA4020 Development Board Application.
#build.bat t 4020 cdb in \target\quartz\mfg\OTP\build\gcc Flash the OTP programmer image to the QCA402x board.
#py -2 qflash.py –comm= <port_number>Connect the QCA402x board to the serial terminal and reboot.
If the OTP programming is successful, the message “OTP update success” appears on the serial console. That indicates that secure boot is on the device.
